
Kali Linux VPS
Offshore penetration testing workstation with pre-configured Kali Linux, anonymous access, and zero logs
- ✓700+ pre-installed security tools
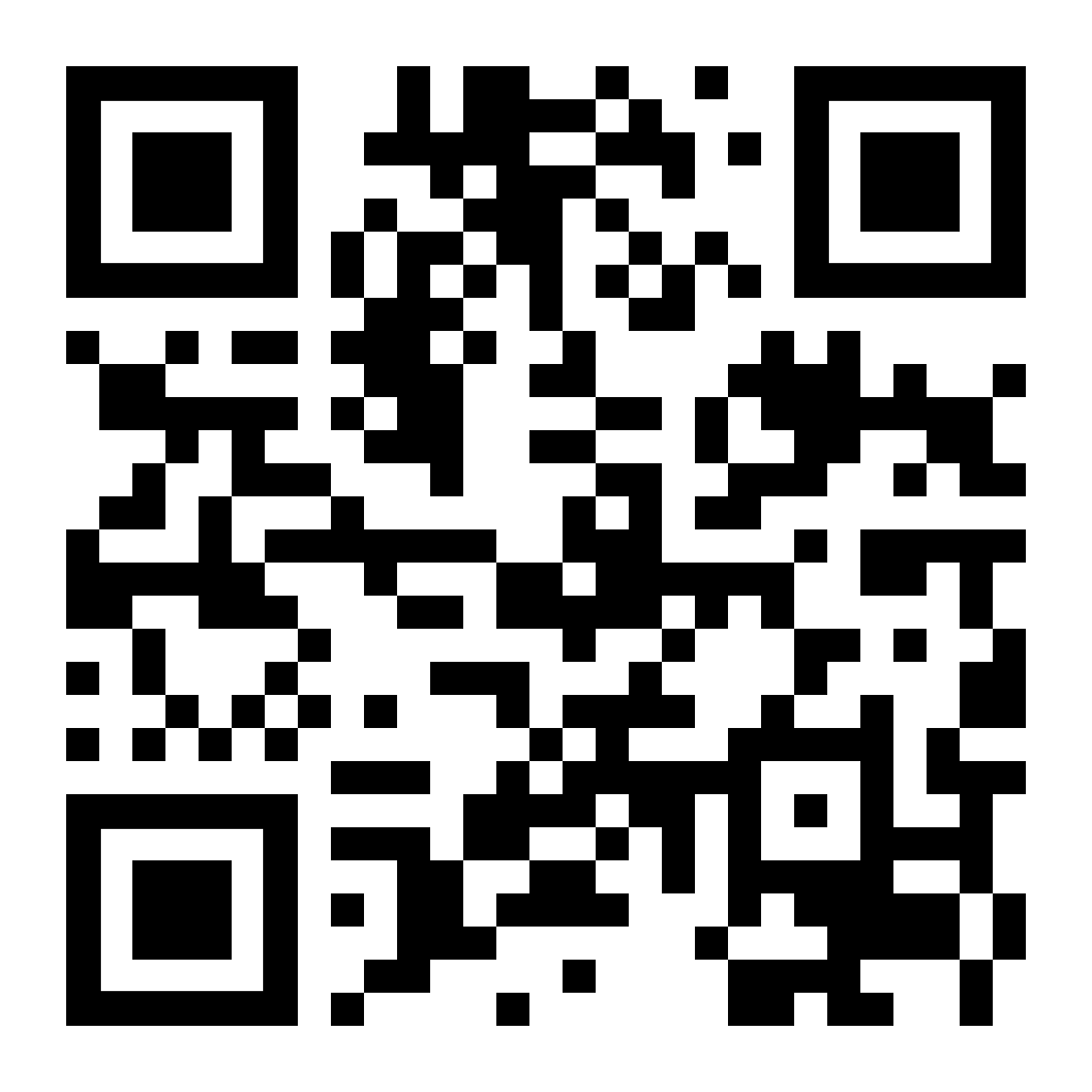
- ✓No-KYC signup & anonymous Tor access
- ✓Dedicated resources & instant deployment
Kali-V1
Ideal for beginners in cybersecurity and students, our Starter Kali Linux VPS provides essential tools and performance to learn the basics of ethical hacking and security testing.
Virtualization
KVM
VCPU
5 x Xeon 5600
RAM
2GB DDR4
Storage
45GB SSD
Bandwidth
200 Mbp/s 3TB
DDoS Protection
Layer 3-4
28.9€ /month
Kali-V2
Designed for professional security analysts and mid-sized projects, this tier offers enhanced power and storage to handle more complex tasks.
Virtualization
KVM
VCPU
8 x Xeon 5600
RAM
4GB DDR4
Storage
60GB SSD
Bandwidth
200 Mbp/s 5TB
DDoS Protection
Layer 3-4
41.9€ /month
Kali-V3
Our most powerful VPS solution for enterprises, offering top-tier resources for advanced penetration testing, security research, and large-scale security operations
Virtualization
KVM
VCPU
12 x Xeon 5600
RAM
8GB DDR4
Storage
100GB SSD
Bandwidth
300 Mbp/s 10TB
DDoS Protection
Layer 3-4
81.9€ /month
Kali-Budget
Experience robust cybersecurity on a budget with our Parrot VPS solutions – affordable yet powerful, designed for aspiring security professionals and cost-conscious users
Virtualization
KVM
VCPU
2 x Xeon 5600
RAM
2GB DDR4
Storage
30GB SSD
Bandwidth
100 Mbp/s 2TB
DDoS Protection
Layer 3-4
14€ /month
Why Choose Our Kali Linux VPS?
Fully-Loaded Security Suite
Dive into a pre-installed suite of security tools, saving time and resources on setup and configuration.
Customizable Workstations
Tailor your VPS to meet specific project requirements with flexible configurations and dedicated resources.
Global Access, Zero Compromise
Connect to your secure workstation from anywhere in the world without sacrificing performance or security.
Seamless Scalability
Easily scale up as your security needs evolve, with plans designed for all levels of use, from individual researchers to large corporations.

Diverse Use Cases:
Security Professionals
Conduct comprehensive penetration tests and security audits with industry-standard tools.
Educators and Students
Use a safe environment for cybersecurity training and education.
IT Consultants
Offer client security services, including vulnerability assessments and network fortifications.
Software Developers
Test application security in a controlled, secure environment
Forensic Analysts
Perform digital forensics investigations with specialized tools available on Kali Linux.
Research Institutions
Engage in cybersecurity research with a platform capable of handling complex datasets and simulations.
Corporate IT Teams
Utilize for regular security checks and internal audits to ensure corporate network integrity.
Frequently Asked Questions
Transparent answers to help you choose with confidence
What is a Pentest Workstation?
A Pentest Workstation is a pre-configured Linux server running Kali Linux or Parrot OS, designed for penetration testing, security research, auditing, and cybersecurity training. It gives you a ready-to-use environment with common security tools already available.
Who is this service for?
This service is intended for security professionals, pentesters, researchers, students, red teams, and advanced users who need a reliable and private remote environment for offensive security tasks.
What operating systems are available?
We currently offer Kali Linux (latest stable versions) and Parrot OS Security Edition. Custom OS requests may be possible on demand.
Do I get full root access?
Yes. You receive full root access to your Pentest Workstation. You are free to install tools, modify configurations, compile software, and fully control the system.
Is the workstation ready out of the box?
Yes. The system comes pre-installed with the standard Kali or Parrot toolsets. You can start working immediately after provisioning, without additional setup.
How do I access the Pentest Workstation?
You can access the server via SSH or noVNC/web console (if enabled). This allows access even if network settings are misconfigured.
How fast is the deployment?
Most Pentest Workstations are deployed within minutes after payment. Credentials are provided as soon as the system is online.
Is this service private?
Yes. Each workstation runs in an isolated environment with dedicated resources. We do not inspect tools, commands, or activities inside the system.
Is KYC required?
No. PrivateAlps does not require identity verification. You can order and use this service without providing personal documents.
Are logs or activity monitored?
No. We do not monitor command history, tool usage, scans, or testing activity. Only minimal infrastructure-level metrics are collected for service stability.
Is this service suitable for real pentesting?
Yes, within legal boundaries. This service is suitable for authorized penetration tests, lab environments, training and research, and red team simulations. Unauthorized or illegal activity is not permitted.
Is DDoS protection included?
Yes. All Pentest Workstations include Layer 3-4 DDoS protection at no extra cost.
Can I upgrade resources later?
Yes. CPU, RAM, storage, and network upgrades can be requested at any time, depending on availability.
Is this service suitable for anonymity?
This service is privacy-oriented, but operational anonymity depends on your own configuration (VPNs, Tor, operational security). We provide the infrastructure, not usage guidance.
How much does a Pentest Workstation cost?
Pricing depends on the selected configuration. All plans and prices are listed directly on our website, with no hidden fees.
Privacy-focused hosting solutions with offshore locations, anonymous payment options, and absolute data protection.
GPU Solutions
GPU Servers
VPN
VPN Service
Copyright © 2020 - 2026 PrivateAlps. All rights reserved.