How to Prevent DDoS Attacks: 10 Best Practices
DDoS attack prevention isn't a one-time setup - it's a layered posture you either build before an incident or scramble to build during one. This guide covers 10 best practices for DDoS attack protection: network-level traffic controls, denial of service attack protection tools, and the organizational decisions that determine response time.
Whether you need to know how to stop a DDoS attack that's already running, or focus on preventing DDoS attacks before they start, every practice here is operational and specific.
AI Summary
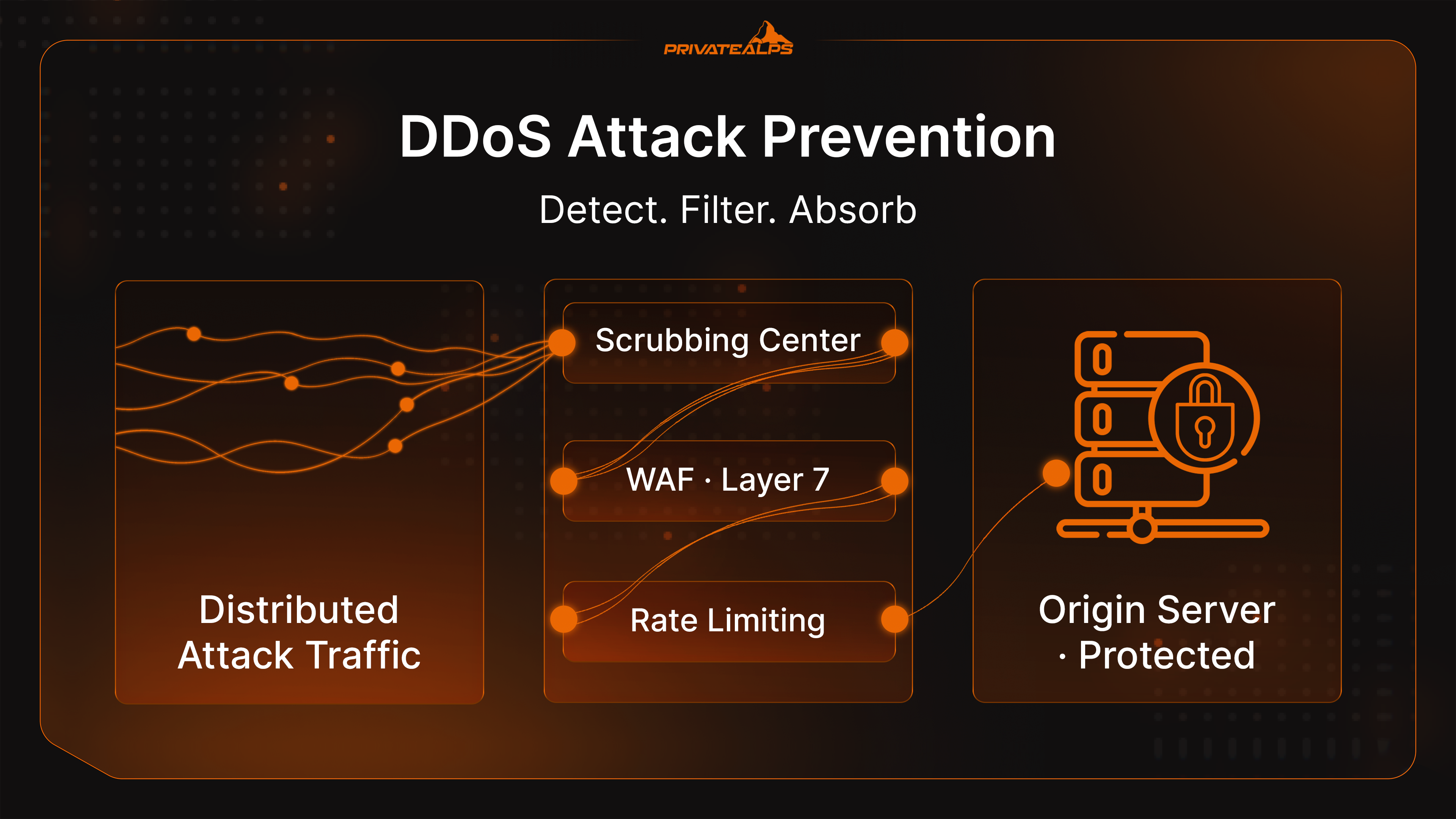
What is DDoS protection, in plain terms? It's the combination of technical controls - scrubbing centers, firewall rules, detection systems - and processes that filter out malicious distributed traffic before it takes down your infrastructure.
The scale problem is real: according to the Cloudflare Q4 2025 DDoS Threat Report, attacks surged 121% in 2025 to 47.1 million incidents, with the single largest attack reaching 31.4 Tbps. According to NETSCOUT H2 2025 DDoS Threat Intelligence Report covering over 8 million incidents, 42% of attacks used 2-5 distinct vectors simultaneously. A single firewall rule or scrubbing service won't cut it. :::
The 10 Best Practices at a Glance
- Use a cloud-based DDoS protection service - and lock down your origin IP.
- Implement rate limiting at the web server, WAF, and API gateway layers.
- Deploy a Web Application Firewall (WAF) for Layer 7 attack coverage.
- Enable anycast network diffusion to spread volumetric attack traffic.
- Configure blackhole routing as an ISP-level emergency fallback.
- Apply ingress and egress filtering (BCP38) to block spoofed-source amplification.
- Scale infrastructure with cloud redundancy, load balancing, and economic DDoS guards.
- Develop and test a DDoS incident response plan with clear escalation paths.
- Conduct regular risk assessments and DDoS simulation testing.
- Train employees and set up ISP coordination in advance.
What Is DDoS Protection and Why Does It Matter?
DDoS protection is a set of technical and organizational controls that absorb, filter, and neutralize distributed attack traffic without disrupting legitimate users. It works across multiple network layers - from packet inspection at Layer 3 to HTTP behavioral analysis at Layer 7 - and covers both pre-attack prevention and in-attack response.
The cost of getting this wrong goes past downtime. Revenue loss, SLA penalties, customer churn. For payment processors and SaaS platforms, 15 minutes of unavailability is a measurable hit. According to the Cloudflare Q4 2025 DDoS Threat Report, the largest attack of 2025 hit 31.4 Tbps - a number that immediately overwhelms any on-premises firewall or mitigation hardware.
The Smokescreen Risk: DDoS as a smokescreen. Attackers flood your network on purpose - not to knock you offline, but to keep your team busy while something worse happens in parallel: Credential theft, lateral movement, or data exfiltration. This pattern is confirmed by Wiz's January 2026 security analysis.
Types of DDoS Attacks You Need to Defend Against
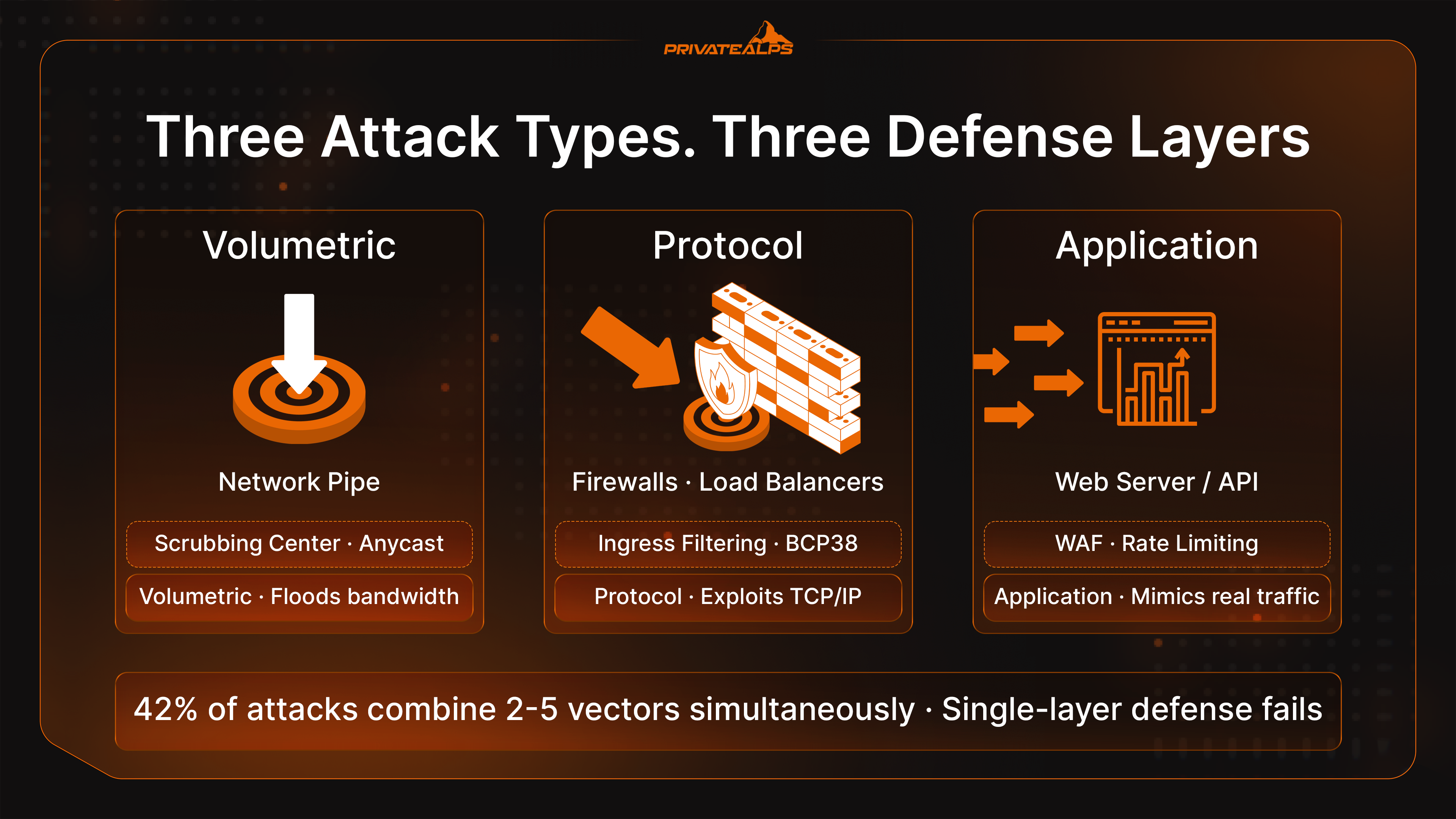
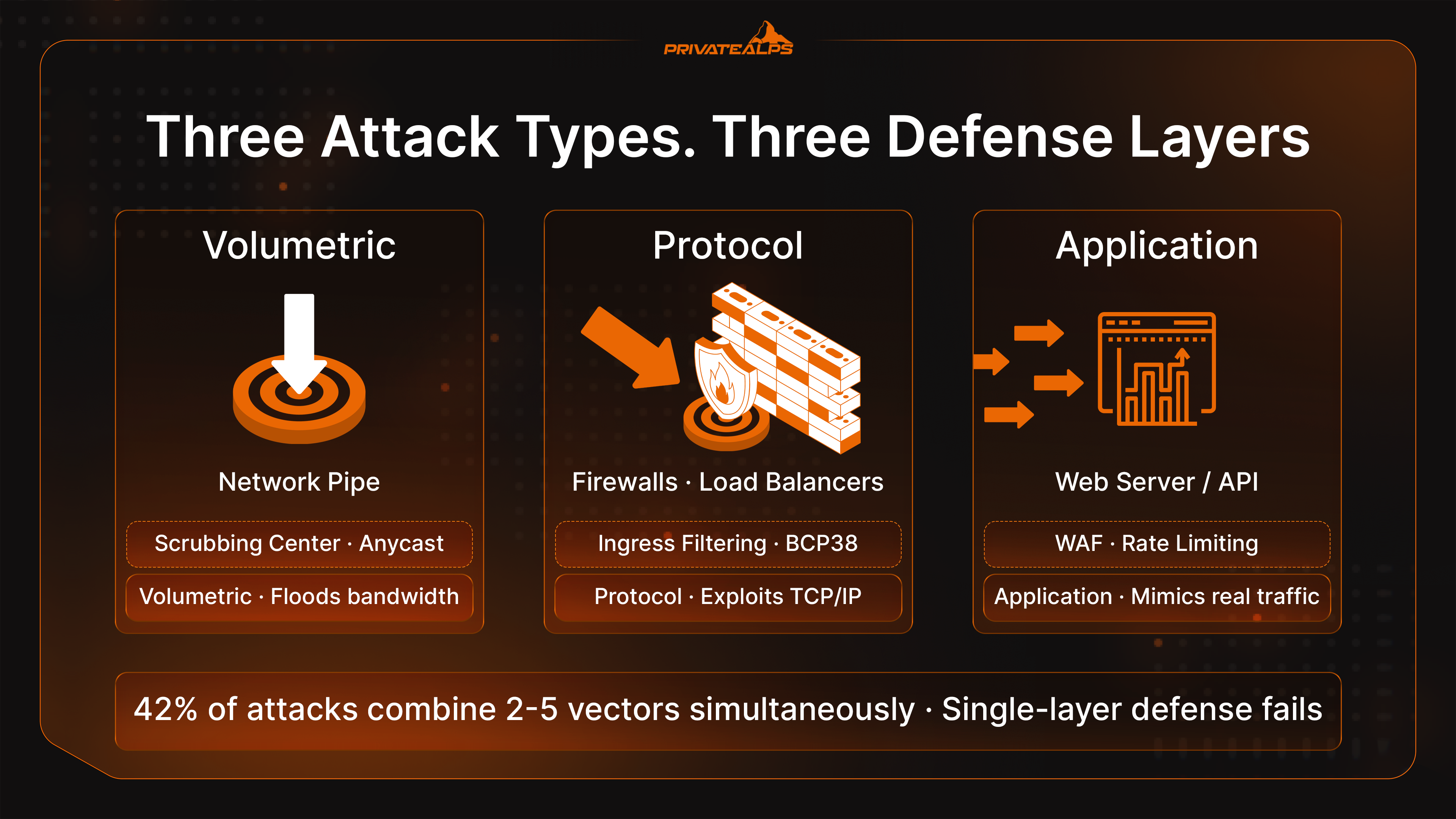
Volumetric, protocol, and application-layer attacks target entirely different parts of your stack. The gap between these layers is exactly what attackers count on.
| Attack Type | Method | Target | Example | Defense Layer |
|---|---|---|---|---|
| Volumetric | Flood bandwidth with massive traffic | Network pipe / uplink | DNS amplification, UDP flood | Scrubbing center, anycast diffusion |
| Protocol | Exploit TCP/IP stack vulnerabilities | Firewalls, load balancers | SYN flood, Smurf attack | Ingress filtering (BCP38), stateful firewalls |
| Application Layer | Mimic legitimate HTTP requests at scale | Web servers, APIs | HTTP flood, Slowloris | WAF, rate limiting, behavioral analysis |
In Q4 2025, network-layer attacks made up 78% of all DDoS incidents. However, HTTP floods and Slowloris bypass network-layer defenses completely because they generate valid TCP connections and keep them open with minimal traffic. Nothing looks obviously wrong until the server runs out of threads.
The NETSCOUT H2 2025 DDoS Threat Intelligence Report found that 42% of attacks combined two to five vectors at once. In November 2025, a botnet was linked to a record 31.4 Tbps attack. In December 2025, the "Night Before Christmas" campaign peaked at 205 million requests per second.
How to Detect a DDoS Attack
Security teams that monitor traffic baselines catch the earliest warning signs - pattern shifts, not service failure - before detection becomes damage control.
Key Detection Signals:
- Sudden bandwidth spike from a narrow IP range or single geolocation.
- Surge in 503 errors or connection timeouts across application logs.
- Unexplained latency increase on internal services.
- Employee connectivity complaints (internal network degradation often shows up first).
- Disproportionate load on one endpoint (e.g., login page or API auth route).
- ISP upstream alerts via automated notifications.
Organic vs. DDoS Traffic: Organic spikes arrive gradually and correlate with launches or newsletters. DDoS traffic appears suddenly, concentrates on narrow URLs, and comes from headless clients with no session depth.
Tooling for Detection:
- NetFlow/IPFIX: Per-flow visibility for traffic anomaly detection at scale.
- SIEM Platforms (Splunk, IBM QRadar): Surface coordinated attack patterns.
- AWS Shield / Azure DDoS: Built-in anomaly detection and automated alerting.
Deep Dive: The 10 Best Practices
1. Use a DDoS Protection Service - and Protect Your Origin IP
Cloud-based solutions route incoming traffic through global scrubbing centers. Malicious packets are filtered before reaching your origin.
CRITICAL: Locking down the Origin IP. If your real server IP leaks, attackers bypass the CDN entirely.
Common leak sources per Red Button’s June 2025 analysis:
- DNS history archives (SecurityTrails, ViewDNS).
- Certificate transparency logs (crt.sh).
- Subdomain enumeration (mail., vpn., ftp.).
- Email headers leaking the IP in
Received:headers.
The Fix: Rotate the origin IP after CDN configuration, restrict firewall to CDN IP ranges, and audit exposure quarterly.
2. Implement Rate Limiting
Rate limiting caps requests per single IP or session. Set it at multiple points: Web server (Nginx limit_req_zone, Apache mod_ratelimit), WAF, and API gateway. A threshold like 10 requests per minute per IP for a login endpoint stops credential-stuffing hybrids without affecting real users.
3. Deploy a Web Application Firewall (WAF)
A WAF (Cloudflare, AWS WAF, Imperva) filters at Layer 7. It catches Slowloris and HTTP floods that mimic browsing. A standard network firewall (Layer 3-4) is completely blind to these patterns. Pair WAF (rule-based filtering) with rate limiting (volume-based cutting).
4. Enable Anycast Network Diffusion
Anycast announces the same IP from multiple distributed nodes. When an attacker floods that IP, traffic routing splits the load across all nodes. This spreads the traffic thin enough to survive.
5. Configure Blackhole Routing (Emergency Fallback)
Blackhole routing sends all traffic aimed at a targeted IP to a null interface. It stops the attack but also kills legitimate traffic.
- Use Case: When an attack threatens the entire upstream link.
- Action: Set up Remote Triggered Black Hole (RTBH) filtering with your ISP _before_ an incident occurs.
6. Use Ingress and Egress Filtering (BCP38)
BCP38 (RFC 2827) drops packets with spoofed source IPs. This cuts off amplification attacks (DNS, NTP, SSDP) at the root. CISA and the IETF treat this as foundational network hygiene.
7. Scale with Cloud Redundancy and Economic DDoS Guards
Auto-scaling and load balancing spread attack traffic. However, this creates a "billing attack" surface.
Economic DDoS: Attackers send just enough traffic to trigger scale-out events, inflating your cloud bill without causing downtime. Defense: Set hard caps on instance counts and budget alerts in AWS/Azure.
8. Develop and Test a DDoS Incident Response Plan
A plan must define:
- Detection thresholds for escalation.
- Specific roles (Who calls the ISP? Who activates scrubbing?).
- Communication templates.
9. Regular Risk Assessments and Penetration Testing
Load test with Locust or k6. DNS infrastructure is a high-priority target because taking it down cuts access to everything else. Follow NIST CSF or ISO 27001 frameworks.
10. Train Employees and ISP Coordination
IT teams need pre-established contacts at their ISP for fast activation. Train teams to treat every DDoS as a potential smokescreen for lateral movement or data access anomalies.
DDoS Prevention vs. DDoS Mitigation
| Approach | Goal | Timing | Example Tools |
|---|---|---|---|
| Prevention | Reduce impact before it starts | Before attack | WAF, rate limiting, BCP38 |
| Mitigation | Reduce MTTR after attack begins | During attack | RTBH, Scrubbing centers |
| Hybrid | Minimize impact and recovery | Continuous | Cloudflare Magic Transit, AWS Shield |
Choosing a Solution: Evaluation Criteria
| Criterion | Why It Matters | Red Flag |
|---|---|---|
| Scrubbing Capacity | Must exceed 31.4 Tbps (2025 record) | Provider won't publish figures |
| Time to Mitigate (TTM) | Seconds matter | No TTM SLA published |
| Layer 3-7 Scope | Must cover both network and app layers | Only "network-level" advertised |
| Pricing Model | Prevent billing spikes | No cost cap on volumetric billing |
What to Do After a DDoS Attack
- Confirm the attack is over: Verify with your ISP. Check that auto-scaling has returned to baseline.
- Look for secondary breaches: Pull authentication and database logs from the attack window.
- Communicate: Send a factual summary to stakeholders. If data was accessed, GDPR Article 33 starts a 72-hour notification clock.
- Post-Incident Review: Document which controls held and update the response plan.
Summary
No single tool stops all DDoS types. Protection relies on three pillars:
- Technical Controls (WAF, Scrubbing, BCP38).
- Infrastructure Resilience (Origin protection, scaling caps).
- Organizational Readiness (Tested response plans, ISP coordination).
PrivateAlps: DDoS Protection at the Infrastructure Layer
PrivateAlps runs Swiss-based VPS and dedicated server hosting with DDoS protection built into the network layer - no third-party scrubbing integration or extra setup required. The mitigation runs at the network edge before traffic reaches your server.
FAQ
What Does an SSL Certificate Do?
An SSL certificate encrypts data channels between user browsers and web servers, making intercepted traffic unreadable. Simultaneously, it authenticates server identity, confirming to browsers that the domain connected is genuinely the one the certificate was issued for.
How Do I Know If a Website Has an SSL Certificate?
The most visible indicators are HTTPS at the start of the URL and a padlock icon in the browser address bar. Clicking that padlock reveals specific certificate details: issuer, validity dates, covered domains, and—for OV or EV certificates—the verified organization name. An HTTP URL with no padlock, or a "broken" padlock indicator, means the connection is either unencrypted or serving "mixed content."
How Much Does an SSL Certificate Cost?
- DV (Domain Validated): Free through Let's Encrypt (renewed every 90 days via ACME automation).
- OV (Organization Validated): Approximately $50–$200 per year from providers like DigiCert, Sectigo, or GlobalSign.
- EV (Extended Validation): Ranges from $150 to $500+ depending on the CA and coverage type.
Note: The price difference reflects the human validation work involved—not the encryption strength, which is identical across all tiers.
Do I Need an SSL Certificate If I Don't Sell Anything?
Yes. Chrome marks all HTTP pages as "Not Secure" regardless of whether you process payments. Google’s HTTPS ranking signal applies to all sites, commerce-related or not. Even a read-only site transmits session cookies and IP address data; encrypting that is now the global standard practice.
What Is the Difference Between SSL and HTTPS?
SSL/TLS is the cryptographic protocol (the "engine"). HTTPS (Hypertext Transfer Protocol Secure) is the result of running HTTP over that protocol. In short: SSL is the underlying mechanism; HTTPS is what users and search engines see in the address bar.
Can an SSL Certificate Expire?
Yes. Every certificate carries a hard "Not After" date. Under the current SC-081v3 validity reduction schedule, maximum validity is shrinking rapidly:
- March 15, 2026: Maximum validity dropped to 200 days.
- March 15, 2027: Reduces to 100 days.
- March 15, 2029: Reduces to 47 days.
An expired certificate produces an immediate, full-page block in all major browsers. These are not warnings users can easily dismiss—they are hard blocks that prevent page loads entirely. Automated ACME renewal is the only operationally viable way to manage this increasing frequency.