What Is a Zero Trust Network?
It’s a security architecture that starts from a blunt assumption: nothing gets trusted by default. Not users. Not devices. Not applications. Logging in doesn’t flip a trust switch. Access keeps getting checked as long as the session exists.
Zero trust isn’t a tool you install or a badge a vendor sells. It’s a way of designing systems so trust is checked every time it matters, not granted once and forgotten.
If you’ve seen how breaches actually unfold, this idea feels obvious. Attackers don’t smash through firewalls anymore. They sign in. Verizon’s 2025 breach data shows that the majority of serious web application incidents still begin with stolen credentials. Once that happens, traditional networks are generous. They assume trust holds, that identity doesn’t drift, and devices stay clean.
Those assumptions are where things break down.
So when people ask: “What does zero trust mean, and why does it matter now?” the honest answer is uncomfortable: the zero trust concept exists because traditional systems are too confident for too long. Zero trust means trust expires. Identity gets rechecked. Devices get questioned. Access gets narrower, not broader, the longer a session lives.
This article explains what zero trust networking is, how a zero trust cyber security approach works in practice, and why it all matters.
Why the Zero Trust Model Emerged: The Collapse of Perimeter Security
Zero Trust didn’t show up because security teams wanted a new framework to argue about. It showed up because the perimeter stopped lining up with how systems are actually built and used. The old idea that you could draw a line around “the network” and trust what’s inside quickly broke, then kept breaking, until it became impossible to defend with a straight face.
What changed wasn’t one technology. It was the accumulation of small, practical shifts that removed any meaningful edge to defend. Zero trust security is a response to that reality, not a trend cycle.
What Changed in Network Architecture
Networks stopped being places and became paths.
Applications moved to SaaS platforms the business doesn’t own. Workloads spread across multiple clouds. Internal tools started talking directly to external APIs. Employees brought personal devices. Contractors came and went. Hybrid environments became normal, not transitional.
In that setup, the assumption of a defensible perimeter collapses. There is no single “inside.” Identity becomes the only consistent signal that travels with users, devices, and workloads across environments. The zero trust model fits systems that are distributed by design, not bolted together behind a firewall.
Threat Landscape Drivers
Attackers adapted to this faster than most defenses did.
Credential theft became the dominant entry point because it works. Verizon’s 2025 DBIR shows that the majority of serious web application breaches still start with stolen credentials. Once attackers authenticate successfully, edge defenses step aside. Authentication succeeds, trust is granted, and nothing meaningful reinspects what happens next.
Insider risk, malicious or accidental, follows the same pattern. Authentication answers “who logged in,” not “what should they be allowed to do right now.” Lateral movement thrives in networks that treat access as a one-time decision.
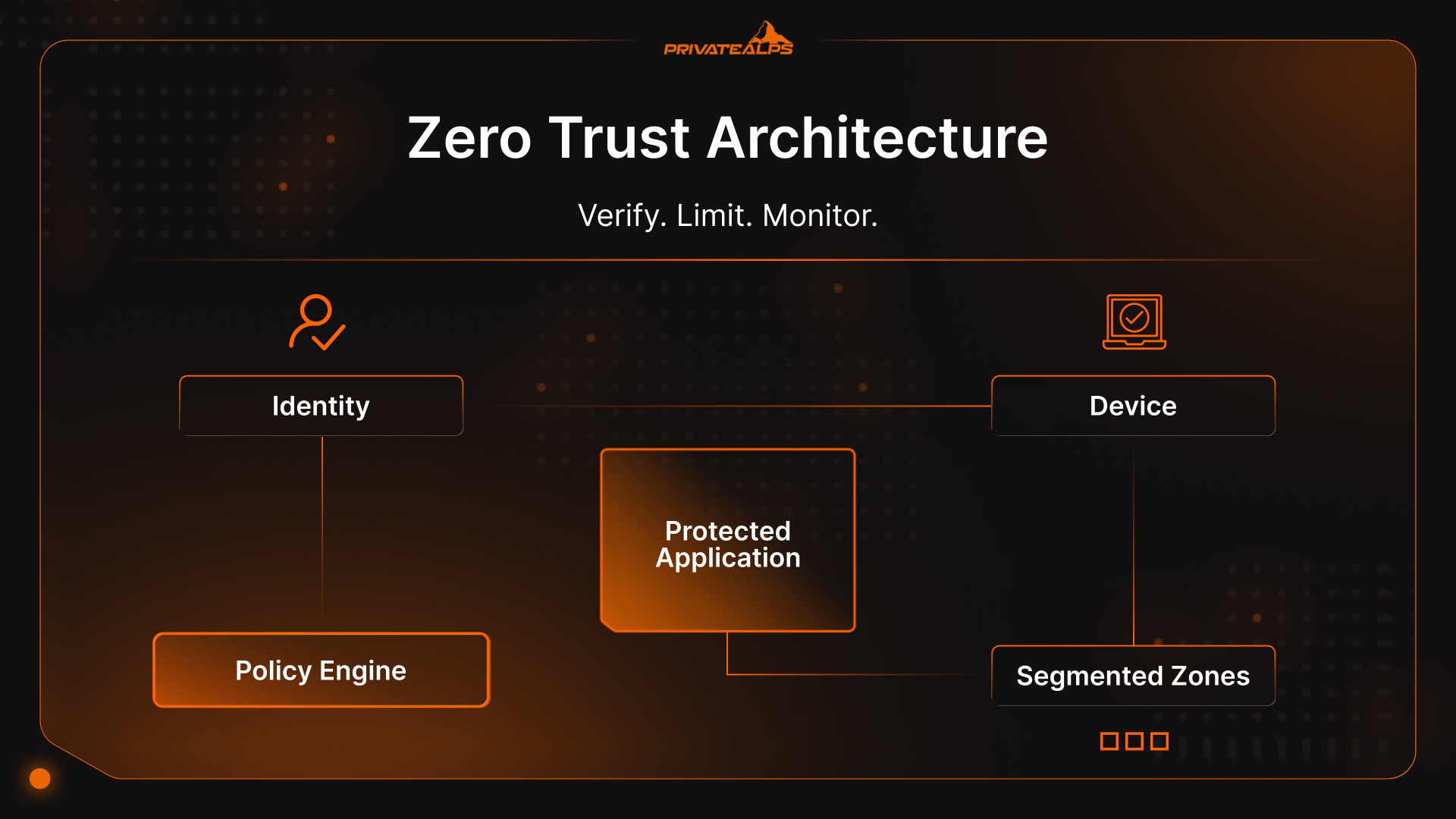
Core Principles of Zero Trust Architecture
Zero trust security principles aren’t values or slogans. They’re rules systems have to follow if zero trust security is going to hold up under pressure.

- Verify explicitly: Every access request has to be evaluated using real signals: - identity, device state, location, behavior, and the sensitivity of what’s being accessed. If the inputs change, the answer can change too. That’s the baseline for zero trust security in practice.
- Least privilege access: Access should stay narrow, specific, and temporary. People and services get what they need to do the work, then it’s gone. The longer access hangs around, the more trouble it causes.
- Assume breach: Systems should act as if someone’s already inside somewhere. That mindset forces limits on how far damage can spread, slows sideways movement, and brings odd behavior to the surface sooner. The zero trust model works because it expects failure instead of treating it like an edge case.
- Micro-segmentation: Networks are split into small, isolated zones around applications and workloads, not flat internal spaces. Even authenticated users don’t get free movement. When something breaks, it breaks small.
- Continuous validation: Trust decays. Devices drift out of compliance. Behavior changes mid-session. Zero Trust systems keep checking and can revoke or step up access when risk rises. One-time approval is the thing attackers count on most.
- Context-aware decisions: Access decisions should reflect what’s happening right now: time of day, unusual behavior, location changes, sensitivity of data. This is how zero trust networking stays usable without being naïve.
- End-to-end encryption: Data should be protected in transit regardless of where it flows. Encrypted connections reduce reliance on “trusted networks” and force verification at endpoints instead of invisible middle layers.
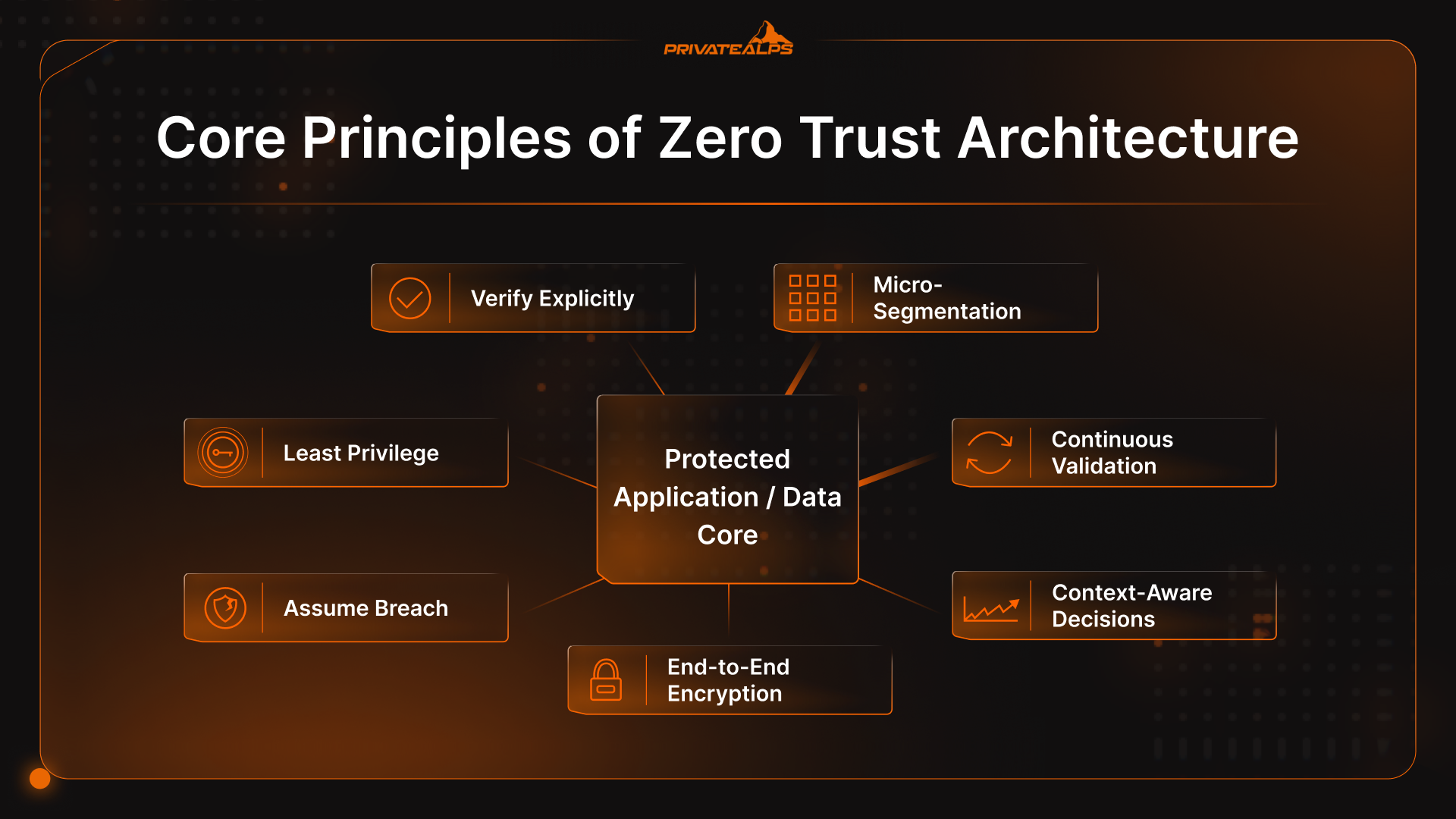
Key Components of a Zero Trust Network
The zero-trust security model only holds together if the architecture can enforce decisions everywhere trust likes to sneak in. That requires specific building blocks, each doing work older networks either skipped or buried behind assumptions. This isn’t about buying tools. It’s about having the right functions in place, whether you call them out explicitly or not.
Core Components of a Zero Trust Network
| Component | What it does | What it replaces or fixes |
|---|---|---|
| Identity and Access Management (IAM) | Verifies who or what is requesting access and what they’re allowed to do | Network-based trust and shared credentials |
| Device trust and posture checks | Confirms device health and compliance before and during access | Blind trust in “managed” or internal devices |
| Network micro-segmentation | Limits lateral movement between workloads and services | Flat internal networks and coarse VLANs |
| Policy engine | Evaluates access decisions in real time using context and risk | Static access rules and one-time approvals |
| Policy enforcement points (PEPs) | Enforces decisions at gateways, agents, APIs, or sidecars | Centralized choke points only |
| Continuous monitoring and analytics | Detects abnormal behavior and adjusts trust dynamically | “Login once, trust forever” models |
Identity and Access Management (IAM)
Identity is the closest thing modern systems have to a perimeter. People have identities. Services do too. So do APIs and background workloads. IAM is what keeps those identities usable as things move between cloud platforms, SaaS tools, and on-prem systems, without access logic breaking every time something shifts.
Device Trust and Posture Assessment
Credentials alone don’t tell you if a request is safe. Device posture fills that gap.
Posture checks look at signals like operating system version, patch level, encryption status, endpoint protection, and signs of tampering. Access can be limited, stepped up, or denied based on those signals. This is how the zero trust security model accounts for lost laptops, personal devices, and machines that drift out of compliance.
Network Micro-Segmentation
Micro-segmentation breaks the habit of treating internal networks as open space. Instead of broad internal access, workloads and applications are isolated behind explicit policies.
Unlike traditional VLANs, segmentation follows the workload, not the subnet. Authenticated users don’t get free movement just because they’re “inside.” When credentials are abused, lateral movement stalls quickly. That containment is one of the most practical wins of the zero trust model.
Policy Engine and Policy Enforcement Points
The policy engine is where access decisions are made. It looks at identity, device state, context, and policy rules as requests come in. Policy enforcement points apply those decisions at gateways, endpoint agents, sidecars, or APIs. Decisions stay consistent. Enforcement stays close to the resource. That’s how zero trust security scales without betting everything on one central choke point.
Continuous Monitoring and Analytics
Static access decisions age badly. Behavior changes mid-session. Compromised accounts don’t announce themselves.
Continuous monitoring feeds telemetry: login patterns, access frequency, data movement, back into policy decisions. When behavior drifts, access can tighten or shut down entirely. This feedback loop is why zero trust doesn’t stop at authentication.
Zero Trust vs. Traditional Perimeter Security
Perimeter security tries to decide what’s “inside” and then relaxes. Zero Trust keeps deciding, continuously, and it scopes access to resources instead of handing out network presence.
| Category | Traditional perimeter security | zero trust / zero trust security |
|---|---|---|
| Trust model | “Inside” is treated as trusted after a boundary check | Trust is never assumed; each request is verified and re-verified |
| Access control method | Network-centric (VPN to the network, broad internal reach) | Resource-centric (per-app/per-resource access, least privilege) |
| Network visibility | Focus on north–south traffic at the edge | Stronger east–west visibility: internal service-to-service traffic and session behavior |
| Scalability | Scales poorly with hybrid, SaaS, multiple clouds | Built for distributed systems; identity and policy travel across environments |
| Breach containment | Often weak once an attacker is inside; lateral movement is common | Designed to limit blast radius via micro-segmentation and scoped sessions |
| Remote access handling | VPN expands internal attack surface to remote users | ZTNA-style access reduces exposure by connecting users to apps, not networks |
Traditional perimeter security still has a role (you still need edge controls). The point is that perimeter models struggle when identity compromise is the common entry point. If attackers can sign in with stolen credentials, the perimeter doesn’t help much.
Zero Trust Network Access (ZTNA): The Core Technology
When people ask: “What is zero trust networking?” they’re usually asking about the tech first.
ZTNA isn’t “Zero Trust in a box.” It’s one access pattern that makes a zero trust security model workable, especially for users who aren’t sitting on a corporate LAN anymore.
Think of ZTNA as the enforcement layer. Zero Trust is the idea. ZTNA changes the order of operations.
With older remote access, you connect first and figure out what you’re allowed to do later. ZTNA does the opposite. Identity is checked up front. Device health is evaluated. Policy is applied. Only then is a connection created, and it’s created to a specific application, not the network behind it.
There’s no internal IP address handed out. No implicit reach into adjacent systems. Each session is narrow by design and watched while it’s active. If posture degrades or behavior shifts, access can change midstream. That flow is the clearest answer to “What is a zero trust network” when people want something practical instead of conceptual.
ZTNA vs. VPN: Key Differences
VPNs assume that once you’re in, you belong. ZTNA assumes that assumption will eventually be wrong. That difference is why teams asking “what is zero trust in cyber security” design often start here.
| Category | VPN | ZTNA |
|---|---|---|
| Access scope | Broad internal network access | App- or resource-specific access |
| Attack surface | Exposes internal network paths | Internal apps stay hidden |
| Trust behavior | Trust granted after connection | Trust reassessed during the session |
| Scalability | Central bottlenecks, brittle at scale | Designed for distributed users and apps |
| User experience | Full tunnel, often slow or unstable | Direct app access, usually lighter |
| Deployment model | Fixed gateways | Distributed or cloud-based enforcement |
ZTNA Deployment Models
There are two common patterns, and most environments end up using both.
Agent-based ZTNA runs on managed devices. It gives you richer posture signals and tighter control, which fits employees and long-lived endpoints.
Service-initiated, or clientless, ZTNA relies on identity and browser access. It’s useful for contractors, partners, and short-lived access where installing software isn’t realistic.
Neither model is “more Zero Trust” than the other. The zero trust model works when access matches risk, not when everything is forced through the same path.
Zero Trust and SASE: Architectural Integration
Zero trust and SASE get tangled up because they tend to arrive together. Teams roll them out at the same time, vendors pitch them in the same breath, and suddenly they sound interchangeable. They aren’t. They solve different problems, and confusing the two usually leads to awkward design choices later.
Where SASE and Zero Trust Overlap
SASE is a delivery framework. It bundles networking and security services and pushes them closer to users and applications, usually through a cloud-based edge. Zero trust is the logic applied inside that framework.
Most SASE platforms end up applying Zero Trust ideas whether they call it that or not. ZTNA decides who can reach an application. Secure web gateways watch outbound traffic. CASB rules shape how SaaS gets used. Firewall-as-a-service covers baseline network filtering.
Together, these pieces make it possible to apply zero trust security consistently without dragging traffic back through a central data center.
The key distinction is this: SASE answers where controls live and how they’re delivered. The zero trust model answers when and why access should be allowed. You can deploy SASE without strong Zero Trust logic, and you can apply Zero Trust principles without a full SASE stack. They overlap because modern environments usually need both.
When to Consider SASE for Zero Trust
SASE makes sense when the architecture itself is already distributed.
If your workforce is spread across regions, your applications live in multiple clouds, and SaaS traffic dominates, centralized security starts to feel slow and fragile. SASE helps enforce zero trust security closer to users, reducing latency and operational sprawl.
It’s also useful when teams are trying to collapse a pile of point solutions. Organizations with separate VPNs, web proxies, CASBs, and firewalls often struggle with inconsistent policy. A SASE approach can simplify delivery while still honoring zero trust security principles underneath.
What SASE doesn’t do is define trust for you. That part still requires clear policy, clean identity data, and discipline.
Benefits of a Zero Trust Network
After asking “what is a zero trust security model?” most people start questioning the value. Right now, about 82% of companies have adopted a zero trust model. That wasn’t because it sounded elegant. It was because the model makes certain problems become easier to control, measure, and explain when something goes wrong.
Key outcomes organizations see include:
- Smaller blast radius during incidents: A compromised account or device can only touch what it was already allowed to touch. It doesn’t fan out across the environment.
- Faster detection and response: Continuous checks make behavior drift harder to ignore, which shortens investigations and reduces how long attackers linger.
- Clearer access accountability: You can see who accessed something, under what conditions, and which rule allowed it. That level of clarity matters when things unravel.
- Reduced reliance on network location: Where someone connects from stops carrying so much weight, which makes remote and hybrid setups easier to reason about.
- More predictable access control: Rules live in policy instead of half-remembered firewall changes or inherited permissions no one owns anymore.
- Lower impact from credential theft: When access is narrow and short-lived, leaked credentials don’t go very far.
The common thread isn’t perfection. It’s control. A zero trust network makes failures smaller, more visible, and easier to contain.
What is Zero Trust For? Zero Trust Use Cases
Zero Trust matters most where trust used to be assumed without much thought. These are the scenarios where the model earns its keep.
Securing Remote and Hybrid Workforces
Remote work didn’t just move people outside the office. It stripped location of any real trust value. Zero trust responds by tying access to identity and device condition instead of network placement. Users connect to individual applications, not the internal network. Exposure shrinks without forcing everyone through a fragile VPN setup.
Protecting Against Ransomware
Ransomware spreads by moving sideways. Zero trust is built to slow that down and limit how far it can go.
Strong identity checks reduce the chance of initial access. Micro-segmentation limits where compromised accounts can go next. Continuous validation means abnormal behavior can trigger access changes before encryption fans out across the environment. The goal isn’t to prevent every intrusion. It’s to stop one mistake from turning into a company-wide outage.
Supply Chain and Third-Party Access
Vendors and contractors usually need access fast, and they usually don’t need it for long. Traditional setups handle this badly. They grant wide permissions to keep things moving, then forget to take them back. Zero trust handles it differently. Access is scoped to specific applications, limited in time, and backed by clear rules. If a partner’s credentials get stolen, the fallout stays small. That matters now that supply chain attacks often look exactly like normal work.
IoT and Unmanaged Device Security
Many devices can’t run agents or support modern authentication. Zero trust doesn’t pretend they can.
Instead, it relies on segmentation and behavior-based controls. Devices are isolated, allowed to communicate only where necessary, and monitored closely. If something behaves oddly, it doesn’t get the benefit of the doubt. This is one of the few practical ways to manage risk in environments full of non-standard hardware.
Multi-Cloud and SaaS Security
Multi-cloud environments break assumptions fast. Different networks, different controls, same users.
Zero trust applies consistent identity and policy across cloud providers and SaaS platforms. Access decisions don’t depend on where an application runs. Identity federation and centralized policy help avoid gaps that appear when each environment is secured in isolation.
How Zero Trust Works in Practice
People looking for a zero trust meaning often find the concept abstract, until they follow a single request as it moves through the system.
The access flow request looks like this:
- Identity gets checked first: A user or service asks for access. Credentials are validated, but that’s just the starting point. Who this is, what role they hold, and how they normally behave all factor in.
- The device gets a vote: The request doesn’t stand on identity alone. The system looks at the device: patch level, encryption, endpoint protection, signs of tampering. A clean login from a risky device changes the outcome.
- Policy decides, not the network: Policies weigh identity, device state, sensitivity of the resource, and current conditions. This is where most access decisions actually live in a zero trust network, not at the firewall.
- A narrow session is created: If access is approved, the connection is made to one application or service. There’s no general network access handed out, no “you’re inside now.”
- The session stays under watch: Activity doesn’t get a free pass after approval. If behavior shifts, access can tighten or end. Trust is provisional the entire time.
Context-Aware Decision Making
Zero trust decisions change as conditions change.
A login from a new country. Activity late at night. A sudden rush of downloads. None of those mean “shut it all down” by default. They do mean it’s time to reassess. The system can step up verification, limit certain actions, or end the session if needed.
That’s the difference between static security and zero trust networking. Trust isn’t yes or no. It’s adjustable, and it moves with risk.
Zero Trust in Cloud and Hybrid Environments
Cloud and hybrid setups are where most people started asking “what is the zero trust model” first, because old trust assumptions stopped working. Applications shift between environments. Users bounce between networks. Data flows through SaaS tools no one fully controls.
Zero Trust works in these environments because it isn’t tied to location. Identity and policy behave the same whether something runs in a public cloud, a private data center, or a SaaS service. That consistency ends up doing more than any single control ever could.
Hybrid environments also expose friction quickly.
Legacy systems often can’t handle modern authentication. Identity lives in too many places. Segmentation exists in theory but not in enforcement. Under pressure, teams widen access “temporarily” to keep things moving.
Zero trust doesn’t magically fix those issues. It puts a spotlight on them. Teams that move forward treat the rough edges as design problems to solve, not reasons to slide back into blanket trust.
Implementing Zero Trust: Phased Approach
Zero trust never shows up all at once. Anyone claiming they “rolled it out” probably renamed a few controls and stopped there. In real environments, it arrives in chunks, usually pushed forward by something breaking.
Most teams end up moving through the same phases:
- Assess: You inventory identities, devices, apps, and access paths.
- Prioritize: You pick what would hurt the most if it went wrong.
- Pilot: You lock down a small slice. One app. One workflow.
- Expand: You repeat what worked and standardize what didn’t.
- Optimize: You remove friction that doesn’t buy you safety.
For most companies, the best place to start is where failure costs real money or credibility.
Privileged accounts. Sensitive data. Production systems. Finance and identity platforms. These are the places attackers target and the places mistakes escalate quickly. Tightening access here forces clarity early and proves the model works when stakes are high.
Common Implementation Barriers
The same problems show up almost everywhere.
Legacy systems can’t handle modern authentication. Identity data is fragmented. Permissions are far broader than anyone remembers granting. Tooling overlaps. Users push back when long-standing shortcuts disappear.
None of this is surprising. Zero trust security doesn’t create these issues. It just stops hiding them. The teams that accept that move forward. The ones waiting for a clean rollout usually don’t.
Limitations and Criticisms of Zero Trust
Zero trust isn’t a cure-all. Some problems don’t go away just because access is scoped better.
- It doesn’t stop insiders with legitimate access: If someone is allowed to do something and chooses to misuse it, zero trust won’t read their mind. What it does do is keep the damage contained and visible.
- A lot of implementations are half measures: MFA plus a VPN rename doesn’t change much. Broad permissions, stale accounts, and “temporary” exceptions still cause most of the trouble.
- The operational load catches people off guard: Policies need attention. Identity data needs cleanup. Logs pile up quickly. Before things settle down, they usually get louder.
- Legacy systems push back: Older applications don’t understand modern identity or fine-grained access. Exceptions start creeping in, and those exceptions need ownership.
- User experience can suffer if no one’s paying attention: When access feels random or slow, people route around controls. zero trust fails when friction isn’t managed.
Zero Trust lowers risk. It doesn’t replace judgment, ownership, or follow-through.
Zero Trust Frameworks and Maturity Models
Once Zero Trust started showing up in audits and procurement language, frameworks followed. The couple you might know:
- NIST 800-207: NIST SP 800-207 is the baseline most serious zero trust work leans on. It doesn’t prescribe tools or diagrams. It lays out principles: protect everything, grant access per session, and keep re-evaluating trust.
- CISA Zero Trust Maturity Model: CISA’s maturity model explains that zero trust isn’t binary. It breaks the idea into five areas: identity, devices, network, applications, and data, and describes stages from legacy approaches to more mature ones. Most organizations don’t move evenly. Identity might be far ahead of network controls. Data governance might lag everything else. That unevenness is normal.
Beyond that, regulations are still evolving. For many organizations, zero trust didn’t start as a design goal. It started as a requirement.
Executive Order 14028 forced U.S. federal agencies to stop treating zero trust as a talking point and start treating it as something measurable. That same pressure shows up in healthcare, payments, and financial services.
Where Zero Trust Ends Up
Zero trust only works if you stop treating it like a finish line. It’s closer to upkeep. Assumptions age out. Access changes. Systems evolve faster than policies do. The real shift is noticing where trust still happens automatically and deciding whether that still makes sense. The rest follows naturally.
If you want to keep going, the best place to look isn’t tooling. It’s in the access paths no one questions anymore.
FAQs
Is Zero Trust a product or a framework?
It’s a framework. zero trust describes how trust decisions should behave over time. Products help enforce pieces of it, but none of them are zero trust by themselves.
Does Zero Trust replace VPNs?
In many environments, yes. ZTNA often takes their place when the goal is giving users access to specific applications instead of dropping them onto the internal network.
How long does Zero Trust implementation take?
There’s no clean endpoint. Most organizations spend years tightening different parts of the model as identity, devices, and applications catch up at different speeds.
Can small organizations adopt Zero Trust?
Most already are, even if they don’t call it that. Start with identity, MFA, and narrow access. Add more only when something breaks or the risk justifies it.
What is the difference between Zero Trust and ZTNA?
Zero Trust is the approach. ZTNA is one way to apply it, mainly for user and application access. One is the rulebook. The other is a tool that follows it.